Confidentiality and Security
Not all archaeological information can be Open Access. Depending on where you live, State and Federal law may require that certain information remain confidential such as site location. Alternately, you may want to contribute materials to tDAR prior to publication and keep them confidential under embargo until the publication date. tDAR was designed with these requirements in mind.
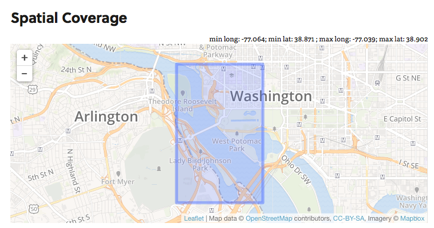
Site Location:
By default, all site locations within tDAR (and shown on maps) are obfuscated when displayed to users, if they are less than 1-mile square. If this is still too detailed a location, users can opt to either draw a box around the county or state, or simply a more general area.
Edit Page – What’s entered; exact coordinates. |
View Page: What users see; obfuscated. |
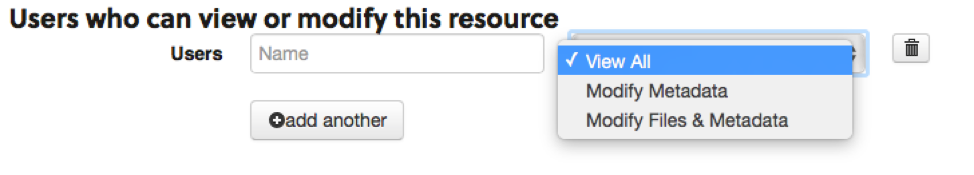
Managing Permissions:
When you create a record, you can control who can download files or edit a record. If a file is confidential or embargoed, you can explicitly grant users permissions to perform more actions.
- “View and Download” permits them to download a confidential or embargoed file.
- “Edit Metadata” permits them to edit metadata on the record (anything but modifying files or permissions on the resource).
- “Modify Files and Metadata” allows them full control over the record including the ability to allow others to view/edit that record.
Granting access to a tDAR record
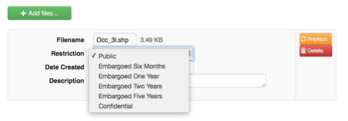
File Access:
When you upload a file to tDAR, you have the ability to control access to the file. Users may specify whether a file is:
- “Public” – anyone can download it
- “Confidential” – only certain people can download it
- “Embargoed” – the file is confidential for a certain period of time, and then becomes public automatically (you’ll be notified a day before, just in case something changes).
Edit Page – Assigning Access Restrictions
|
View Page: Restrictions |
Learn more about tDAR’s security:
Digital Antiquity takes the security of archaeological data seriously. To ensure the user information and archaeological data is kept securely and in accordance with Federal and State laws, we have taken a number of steps. First, data in tDAR is stored on servers hosted at Arizona State University in an access-restricted environment. Second, we use 256-bit or greater encryption to secure data and data transfers. When users are logged into tDAR all communications are also encrypted over SSL using 256-bit encryption. Backups are 256-bit encrypted prior to being sent off-site. Finally, the tDAR application is behind a firewall which protects from some network based attacks, and we regularly test the application for common vulnerabilities and exploits.
tDAR and the servers it runs on are also regularly patched and updated to address security issues and exploits. As part of the software development process, tDAR’s test suite also has a set of tests which we regularly add to focused on testing known exploits, data security issues, and other problems. tDAR must pass all of these tests prior to any update of the production software.